Account setup
A free Bridgecrew account
The Bridgecrew platform will give us visibility, solutions, and alerts from the first line of Kubernetes manifest all the way through to checking the running cluster’s security posture. Sign up or log in to an existing account at https://bridgecrew.cloud
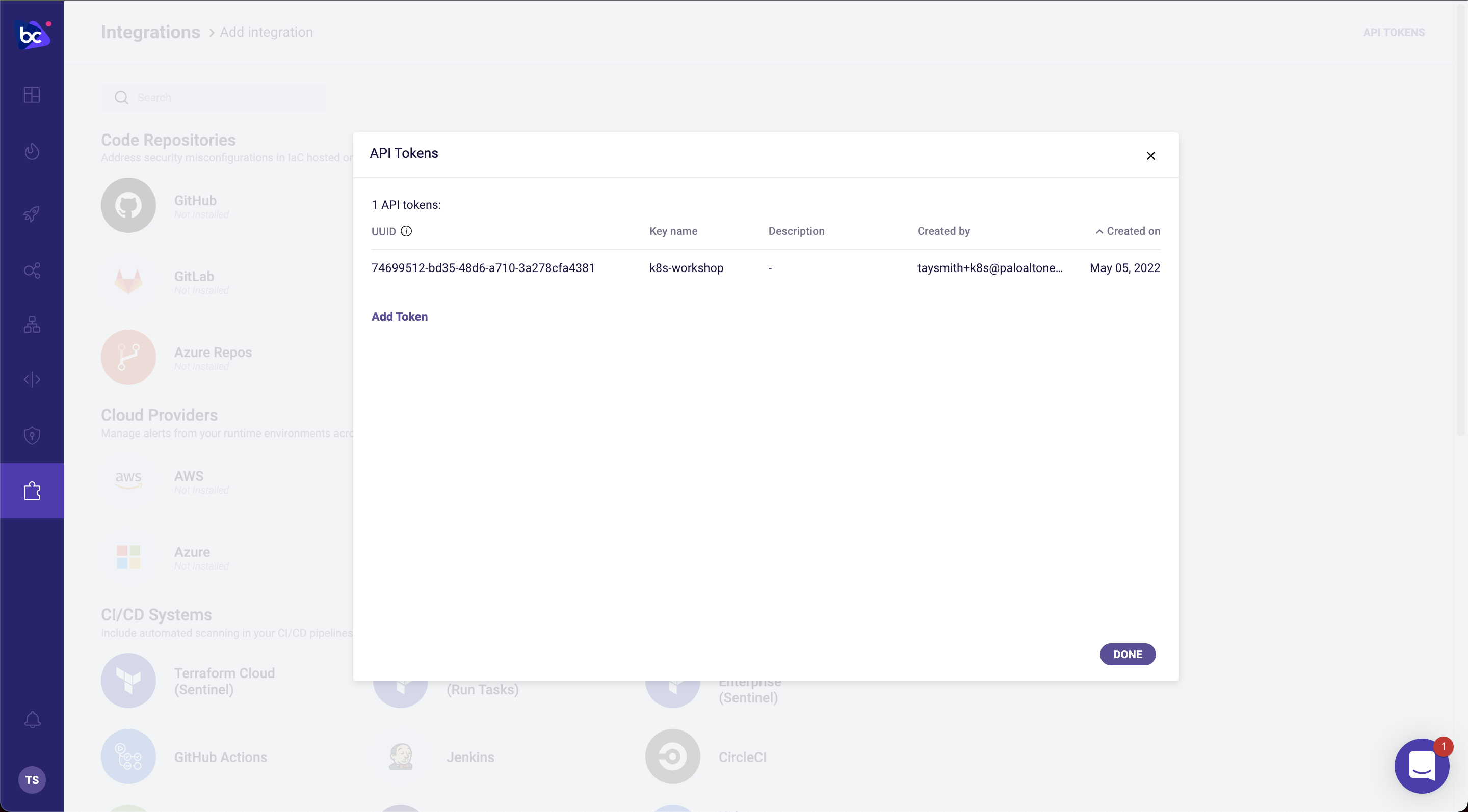
Generate a Bridgecrew API key
Throughout this tutorial, you’ll need to use the Bridgecrew API token. You can access it here or in your Bridgecrew account by navigating to the Integrations tab and selecting API Token. Add a token for the workshop and save it in your notes for later use.
A free GitHub account
You will need a GitHub account to fork and edit our example infrastructure as code (IaC) so that you can automate and fix any Kubernetes issues!
GitHub discourages individuals from having more than one account. If you already have a GitHub account you can follow along with this workshop without worrying about conflict with your private repositories.
Fork KustomizeGoat
This workshop uses our vulnerable-by-design Kubernetes and Kustomize project, KustomizeGoat. This project gives us a base set of deployments we can explore, edit, and remediate without needing to integrate your own code.
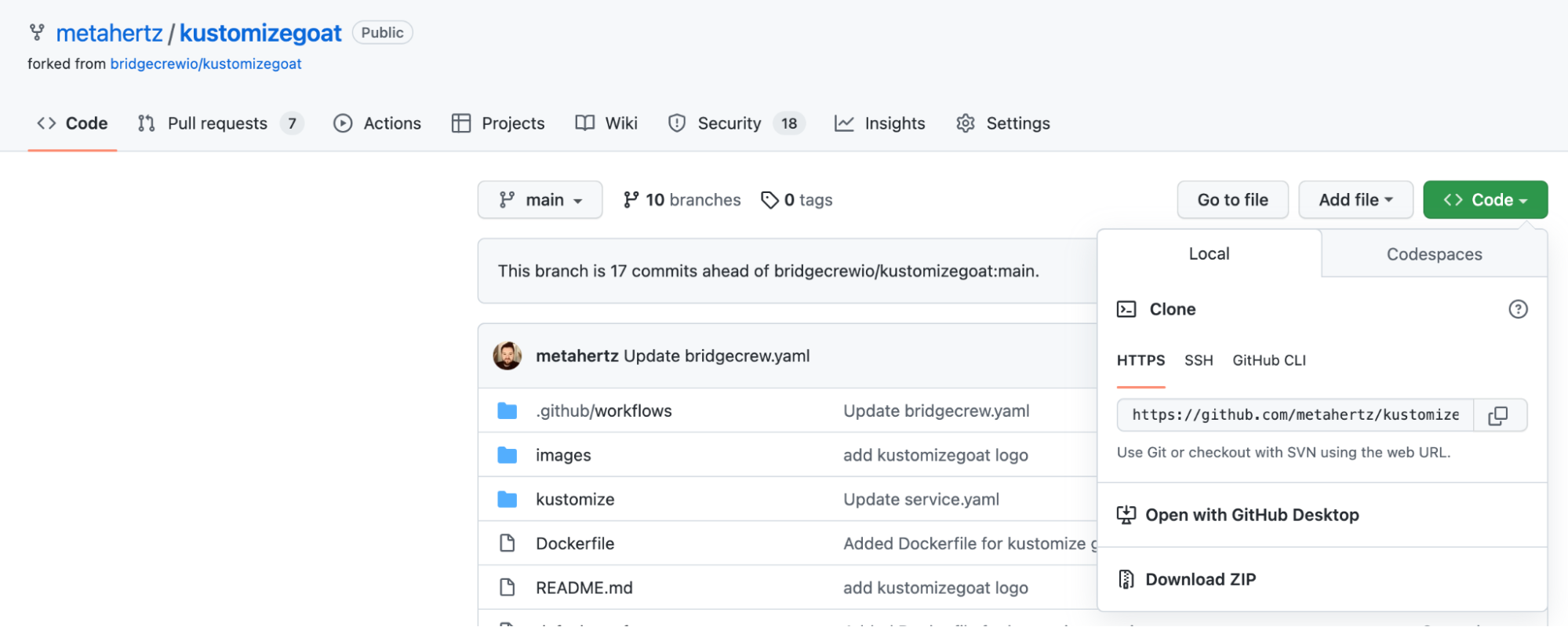
Fork the KustomizeGoat repository on GitHub
To set up your demo environment, we’re going to fork the KustomizeGoat repository.
Head over to the KustomizeGoat repository and fork it using the button in the upper right corner.
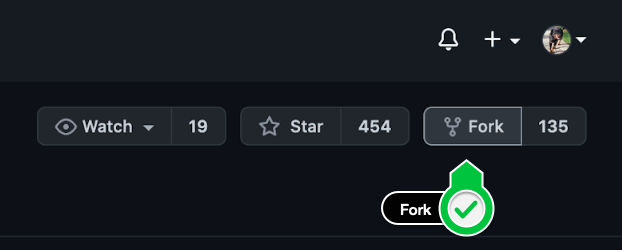
If you have multiple organizations, GitHub will ask which of your orgs to fork into. Choose your personal account by selecting your GitHub username from the list. This will fork the repo.
Note down the URL for this new copy of the repository, also known as the “git clone address”, select “code” and copy the HTTPS address that is shown. The HTTPS address format is:
https://github.com/<your-github-user>/kustomizegoat.git